EDN
We develop a new protective Internet
Welcome
This is the official wiki of the research and software project EDN (Echt Dezentrales Netz - real decentralized network). Our vision is to provide a more secure and confidentiality preserving communication means to billions of people: individuals, families and organisations of whatever format - a new internet fitted with a set of privacy tuned services running on local individual or public infrastructure and meets our standard.
News
We have a new website which addresses potential sponsors. Recently we have presented EDN to the people of Wau Holland Foundation. Thank you for your invitation!
Here is our project diary.
- Note
- .onion addresses can be accessed via Tor Browser Bundle
Status Quo
Centralization, Outdated Protocols
The prevalent digital communication means undermine their users' data integrity and confidentiality starting with
all digital communication of one country going through one or just a few telecommunication providers' servers.
These accumulate data, including metadata, which is the basis to derive people's social graphs, movement patterns and even psychological profiles.
Further centres of data accumulation are services like Facebook, Twitter or Youtube.
They profited by peoples' wish to reach as many people as possible.
This has led them to focus on using certain services - known as the Network Effect - rather than privacy and security aspects.
This not only helped these services grow significantly, but also led
to huge data accumulations in few locations.
These have its own value for several groups and provoke criminal activity to access and misuse it.
When your hardware gets stolen you soon will notice that. It makes a transition from you - the rightful owner - to another one.
Usually data won't be moved just copied. You won't notice the access directly or never if you have entrusted it to another party or let your digital communication flow through a single instance exposing all your meta data.
To make things worse the current internet protocols base on a completely outdated threat model as the Snowden revelations have shown at the very latest.
They are by design vulnerable to a number of attacks.(1, 2, 3).
These open ways to undermine even overlaying structures, such as Tor, deanonymizing its shelter seeking users and hidden services by traffic correlation.
These conditions- the brokeness and centralization- facilitate:
- Censorship: On plattforms and by countries;
- Passive Mass Spying;
- Active Intrusion on a global scale;
It is most likely that patches like overlay networks can only ease the shortcomings of the current internet but not fix it using this vulnerable basis for confidential communication. This may be less critical for high latency networks over the Internet or Sneakernets that do not use the internet at all. Alternative networks, however suffer from the following problems. Their network is unlikely to gain enough users, due to shortcomings in their accessibility and usability. Thus, it will not be attractive for most people wanting to communicating with their friends. Moreover, such a small user group might also jeopardize the users anonymity and privacy, as each user is deemed suspicions and errors in the network stack take longer to get fixed. Finally, this cast doubt on the whole idea of an alternative network. To break this cycle, we think that multiple well tuned secure solutions must be brought together focusing on accessibility and usability, to combine and increase their small user groups and kick start the required Network Effect.
Threat Model
We presume a global active attacker that does automated intrusion such as traffic shaping.We share our threat model with Secushare.
Competitiveness and Lack of Collaboration
Here is our list of Privacy Software Projects.

The privacy and security software landscape is highly fragmented. This has implications for their quality and therefore for their users' privacy and security. We found over 80 Free Software Privacy Projects and this is nowhere near complete regarding this survey. All compete for contributors, funding, users, bandwidth while implementing redundant, often mediocre solutions which is no wonder since most of them lack resources to do it all good. This leads to bad code documentation, which consequently impedes potential help by new developers or researchers finding vulnerabilities and providing more secure solutions. These are some reasons why there is almost no collaboration between the projects although they share the same goals and would benefit from these collaborations exceptionally.
Goal
Regarding the design flaws of the current internet, we believe that a complete new internet providing confidentiality, integrity of communication and censorship-resistance is indispensable. We envision the new stack to be
- Privacy tuned for and delivered with several services
- Convenient and attractive to use, focusing on accessibility and usability
- Able to run on local individual or public infrastructure
- Free Software
The new internet uses the existing infrastructure to form a difficult-to-monitor cellphone/router/computer network. Its communication runs, first and foremost, on top of a combination of WiFi, copper and fibre optics. Moreover, we consider Bluetooth, Ultra Wideband (UWB), red light, UKW and satellite uplinks - shortly all allowed frequencies and means of digital communication.
Criteria for the New Internet
The new internet should meet the following criteria. The quality of security and privacy might vary between the different exposed services. (...).
Services
| public | personal/private | ||
|---|---|---|---|
| Text | Chat of local (neighboring) nodes | To a single person: Chat, Email or SMS | To multiple people: Chat or mailing list |
| Audio/Telephony/Video | Call among locally restricted nodes | normal call | conference call |
| Other formats | ? | ? | ? |
- Social-Networking: Messaging, Micro Blogging, (Video)-Telephony;
- Data Storage (individual, group and public access);
- Searching contents in local and other reachable networks;
- Mirroring contents of the "old" internet;
- Payment system;
- Smart contract (blockchain);
- Collaborative document editing.
Overtaking the Attackers
The arms race between attackers and defenders over data security and privacy on the internet is ongoing. However the conditions are good to overtake the attackers generously and change the game in favor of the defenders by way of variety replacing the broken internet by a combination of cutting-edge technologies:
- New internet protocol stacks: There are new internet stacks among the privacy software projects such as GNUnet, Maidsafe, Net2o and implementations: http://www.irati.eu/ RINA. They have developed privacy aware routing and decentral naming systems for over ten years now. They are waiting for having services set and top of them and evaluated.
- Matured operating systems for embedded devices and wifi-meshnet-routing: It increases the effort of espionage if a computer network is decentralized. One important part of this is even to decentralize local communication by using a wireless network in connection with multiple internet accesses. Open Wireless Communities are existing already for some years. Have developed and optimized their routing algorithms and gained experience. They deploy routers and boards using Linux-based firmwares such as OpenWRT and DD-WRT. GNUnet has already been packet for OpenWRT and has potential to revolutionize Open Wireless communities.
- Authority Free Onion Routing using BRAHMS is on the way.
- Reproducible Builds: "to empower anyone to verify that no flaws have been introduced during the build process by reproducing byte-for-byte identical binary packages from a given source."
Beneficiaries of the New Internet
In the long run everyone will benefit from the new internet, since it is censorship resistant, provides confidentiality and integrity preserving services. It results in:
- Average citizens regaining parts of their privacy, informational self determination, freedom of assembly, secrecy of correspondence and free speech - basic civil rights that ensure and back up our democracies.
- Safer government institutions and companies from espionage and "cyber" attacks.
Use cases are for example online banking, government communication with citizens including tax returns, diplomatic and business communication and journalism.
Approach

We aim to unite the different forces and resources of Free Software projects to achieve what none of them could do alone: Kickstart a network effect and provide a more secure and confidentiality preserving communication means to a significant part of the world-population - a new internet fitted with a set of privacy tuned services. To get there we built bridges by creating a better documentation for circa 20 privacy projects during our Software Documentation Marathon™. It will include a first analysis of the project's security and privacy qualities and recommendations for collaborations between interoperable projects.
On this basis we are able to proceed with the testing of different stacks and a Prototypical Realization of a wifi-mesh-able new internet with multiple integrated services.
Software Documentation Marathon™
We plan a Software Documentation Marathon™, where we document and analyze circa 20 free software projects
Key elements of our work will be to assemble detailed API descriptions of the projects and its modules and to identify and highlight Interoperability between projects.

We will collect the information needed by personal interviews with the privacy project developers.
All the information will be gathered in a standardized way and collected in a semantic wiki providing us with a set of tools to dynamically interconnect, organize and visualize the information.
Beside graphs and images it enables dynamically generated tables or query based searches.
This way our results will be easy to reuse. It will be published under the Creative Commons licence CC-BY-SA.
The Software Documentation Marathon™ delivers the work base for Prototyping and Testing.
- Note
- @Software Documentation Marathon™: We used the ™ just for fun to express that we like the name of this phase very much. Everyone who likes the name too can use it!
Software Documentation Contents
-
Status Quo of the Marathon (progress bar), total and for every single project (3);
-
Basic Information: programming-language(s), software-licence(s), etc. (4);
-
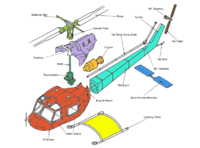
Project Anatomy: Visualization of the Projects' Architecture, description of its components, their functionality, its interaction/communication, link to its code base (5);
-
Unified API Documentation for every project and its modules (we choose one of existing standards) including its privacy, security and performance assertions and preconditions (6);
-
Highlighting Interoperability: intersections where projects could be connected and therefore collaborate or simply share code (7);
-
Known Vulnerabilities and Resistance to a list of attacks and more (+ derivable vulnerabilities) (8);
-
Double Implementations of similar functionality (9);
-
Top Features the projects would like to implement/integrate (that meet hard problems such as anonymity and large scale mesh-networking) (10);
-
Tests performed : Details about tests that have been already performed by the projects
Some properties could be organized like this:
- Claims to provide (list of criteria)
- (Actually provides (list of criteria)-> checked by testing phase)
- Enables (list of services)
- Replaces (list of proprietary software)
- Prevents (list of attacks under (list of conditions))-> threat model (type)-TRIKE
- Interfaces with (ecosystem): ?
- Interconnects with (list of OSI-layers, list of software projects, list of modules)
- Implements (list of modules)
- Is component or standalone (full app) or runs on bare metal
- Runs on Unix like operating systems
Benefits
The documentation leads to:
- Better maintainability of code, deployability without big effort by the projects;
- Saving ressources ((wom-)men-power, in best case bandwidth and computational cost;
- Faciliate collaboration between projects in order to solve hard problems such as anonymity but also provide other desired features and better usability;
- Ensuring security more easy by using proven modules;
- A thorough Knowledge-base for researchers and developers that spares valuable time to get to know other projects without reading tons of code;
- A thorough Knowledge-base for foundations in this field;
Combination-Prototyping and Testing

The Software Documentation Marathon™ delivers our working basis to preselect a combination of projects or modules that are interoperable and meet our standard. In this phase our objective will be to create prototypes and test them in a generic manner on a virtual and a real testbed.
Testing Objectives:
- Deployability and Configurability
- Scalability
- Reliability: Under normal conditions, hard conditions, attacks: Percentage of completed/successful processes.
- Performance: How does a complete process take in worst case?
- Lightweight: Payload and program size
- Security and Privacy : Resists a list of attacks in percentage.
-
Resilience
-
Performance
-
Networking overhead and size of program
Testing:
- One or two services on different stacks
- New combinations of modules for the stacks
- Multiple network configurations with respect to specific situations (e.g., attack scenarios, dense and distant mesh, internet connected nodes)
- Multiple services on one stack
Test Results Reveal
- Best stack for given service and situation
- Optimal network configuration for the different use cases
- Sweet spots between scalability, performance, and privacy and security
Best Current Practice Recommendation
The following is an essence of a Best Current Practice Recommendation.
-
Instant Messaging: Ricochet
-
Filesharing: Tribler
-
Asynchronous Messaging: Bitmessage
-
We add this one for Browsing: Tor-Browser-Bundle
Community and Crew
We are stakeholders of GNU consensus and allies of the #youbroketheinternet project. To our crew belong software architects, a student of Fine Arts, Privacy Project developers and Privacy and Security researchers.
Contact
Be with us!
Write us in Bitmessage:
BM-NBqqoMzajZNXQru2Kz4JXqq6RbsEmeuL
Email: demos et posteo dot de, GPG, Fingerprint:
9A0E 7D84 0D22 F15A 3FE3 4756 2DB7 1A63 B093 2843
Picture References
- CCO "Six pigs" by piotr siedlecki
- CC-BY-SA "Gingerbread Puppeteer" by theyogre, decolored by dmos
- CC-BY-SA "Paper Trails" by Leland Francisco
- CCO "Delaunay Triangulation" by Inductiveload
- CC-BY-SA by Picol, arranged images by dmos with filsharing image extracted from a batch by FSF
- CCO, "Bridge"
Picture References SDM
- CC0 "player-running-black-and-white" by Clker FreeVectorImages
- CC-BY-SA "Interview Without Speech Bubbles" by GSJ
- CC-BY-SA Dmos
- CC-BY-SA "Supreme Shapes" by 10binary, colored by Dmos
- CC-BY-SA "Helicopter Anatomy" by Richard Wheeler(Zephyris), colored by Dmos
- CC-BY-SA "documentation" by OpenIcons, modified by Dmos with "sourceCode" by SimpleIcons
- CC-BY-SA "Open Innovation - off" by berteh, colored by Dmos
- CC-BY-SA "New Haldi" by EvgenyGenkin, colored by Dmos
- CC-BY-SA "BikeWheel" by carlitos
- CC-BY-SA "Tanabata-Wish-Tree"by uroesch, recolored by Dmos